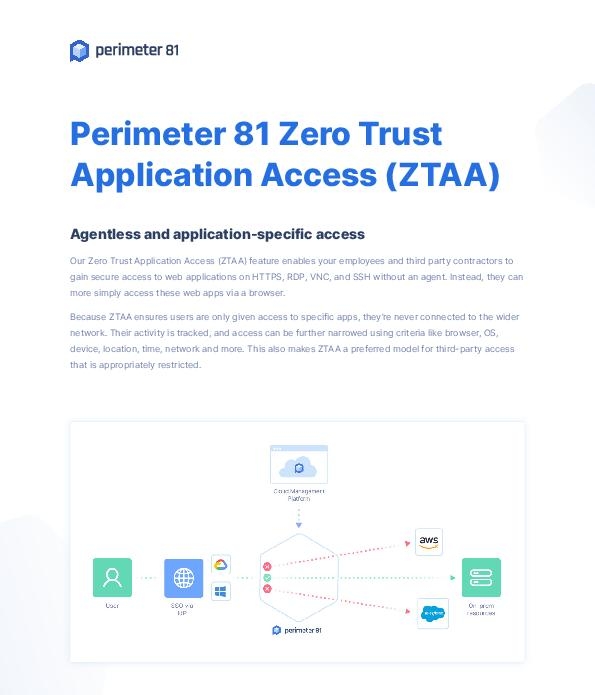
Perimeter 81 Zero Trust Application Access
With Perimeter 81 Zero Trust Application Access Employees and third-party contractors can gain secure access to web applications on HTTPS, RDP, VNC, and SSH quickly and easily via a browser. How simple is that? Read the solution brief to learn why ZTAA is a preferred model for third-party access. DM us to discuss how Perimeter 81's No agent-No problem ZTAA can improve your network security.